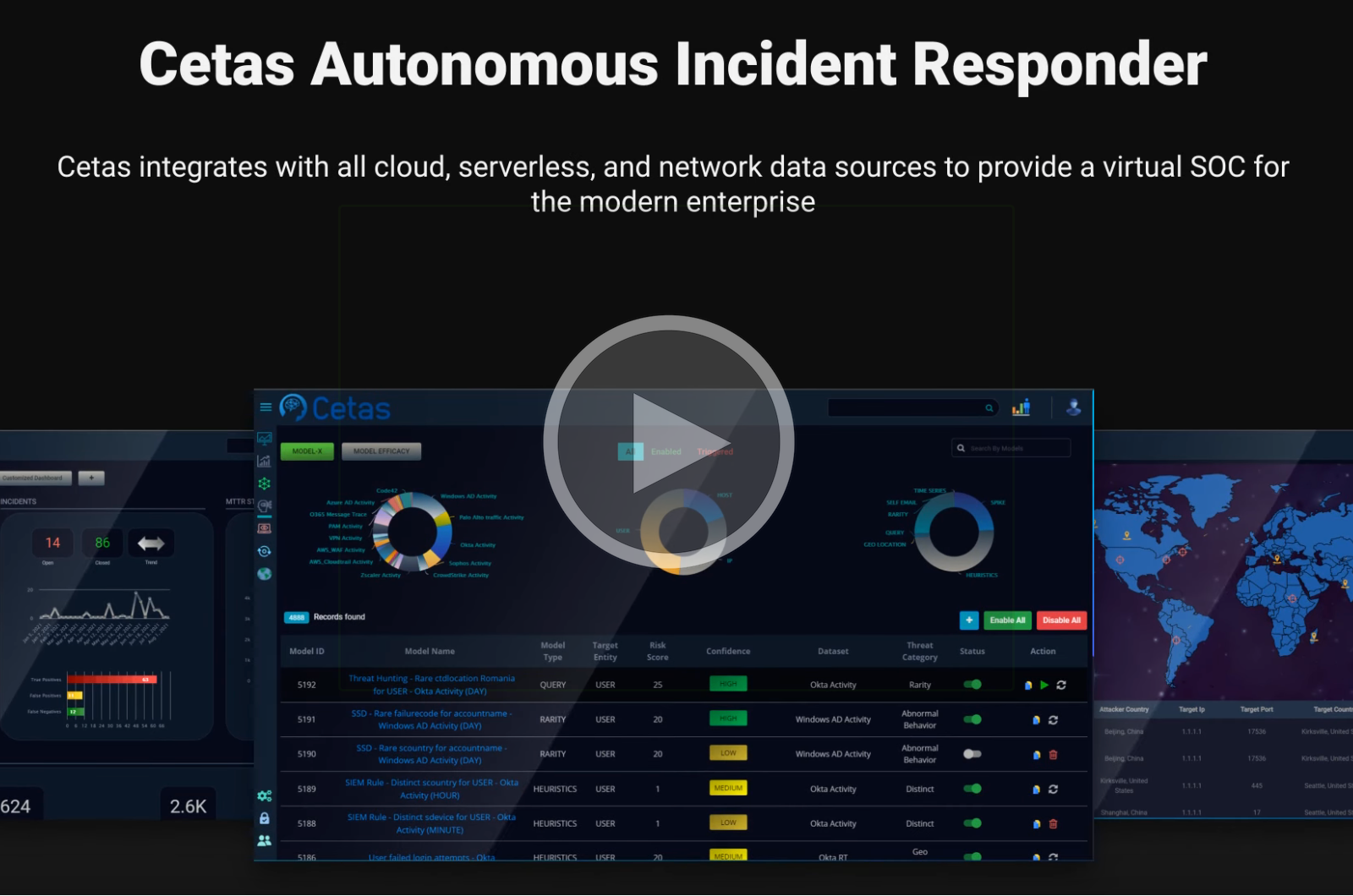
Modernize Your SOC
Optimize Security Operations by Automating Threat Detection, Investigation and Response
Bringing Autonomous Cybersecurity to Life
Virtual Security Engineer
Build threat detection models in minutes with a no-code platform, leverage state of the art AI to create new models at scale autonomously, and gain >99% detection coverage across the cyber kill chain.
Digital Investigator
Prioritize critical alerts and eliminate false positives with automated investigation. Utilize visual timelines along with associated context for automated response and remediation.
Proactive Threat Hunting
Proactively search for undetected threats and anticipate attacks with our AI-driven, no code threat hunting platform and built-in threat intelligence integrations.
Discover Our Platform
Automate threat detection and response, and maximize the productivity and effectiveness of your security teams.
Provide holistic cloud security and protect your data, applications, and users from any threats in real-time. Continuously assess your cloud security to monitor threats, improve visibility and eliminate blind spots to build an effective enterprise-wide incident response strategy.
Identify threats in real-time with AI-driven models, and make better use of available resources by automating threat detection to save time and money. Proactively find and act upon undetected threats with the help of automated models.
Augment your security teams with AI/ML technologies to be quick and accurate in threat detection and remediation. Eliminate noise due to false alerts while focusing on critical risks by effective triaging.
Centralize data flowing in from varied sources such as applications, networks, endpoints, etc., so it can be analyzed to build visual timeliness with associated contexts, making it easier to investigate threats. Leverage the stored data to develop models and proactively hunt for threats.
Customer Praise
Frequently Asked Questions
What is cybersecurity?
Cybersecurity also called Information Technology Security is a practice of protecting and securing systems, applications, data, networks, and devices from cyber-attacks. These attacks are intended to be malicious and are aimed at gaining unauthorized access to systems and networks, theft of sensitive information, etc. to extort money or cause disruptions.
What are cybersecurity solutions?
Cybersecurity solutions are technologies and services that help safeguard businesses from cyberattacks that cause risks like business disruption, reputation damage, data theft, application downtime, etc.
What is autonomous cybersecurity?
Autonomous Cybersecurity is the application of the most advanced AI/ML technologies to automate cyber threat detection, response, and remediation enhancing cyber defense. Cyber threats are evolving at an unimaginable pace and autonomous cybersecurity is an effective way to handle these complex and increasingly sophisticated attacks.
Get Regular Updates
Get updates about our products and services direct to your inbox.
About Us
Product
Solutions
Partners
Resources
Copyright © 2022 Cetas